Digital Traceability at Aerospace Standards: Manufacturing Execution System (MES) Model
Designed strictly according to the zero-tolerance standards of the Aerospace and Defense industry, this Manufacturing Execution System (MES) secures end-to-end hardware traceability across complex assembly lines. The system fully digitizes the physical lifecycle, spanning from raw inventory management to sub-assembly cycles and conclusive platform integrations. The framework natively mandates unique hardware identification (UUID serialization), robust separation of duties via strict RBAC matrices, and deterministic inventory allocation mapped via FIFO algorithms. Operating cleanly past the prototype phase, the system is actively ready for immediate field pilot deployment and seamless integration loops with corporate ERP macro-services (SAP/Oracle).
💡 Sectoral Scalability: Structured directly utilizing rigorous Aerospace compliance benchmarks, this architecture possesses the inherent flexibility to be directly scaled horizontally into automotive, heavy industry, and generalized industrial machinery production bands without necessitating fundamental architectural alterations.
Project Portfolio
|
Parameter |
Value |
|---|---|
|
Category |
System Integration |
|
Delivery Type |
Software System Architecture / PoC |
|
Status |
Proof of Concept |
|
Role |
Integration Architect |
|
Scale / Scope |
End-to-End Assembly Traceability, API Development |
Current Situation and Problem
Context: The integration environments of autonomous platform products (TB2, AKINCI, etc.) within the defense sector mandate exceptionally unyielding traceability compliance regulations. Every individual physical hardware unit populating the factory grid constitutes an obligatory audit record—demanding absolute clarity regarding which approved procurement batch it originated from, which specific operator configured it at which station, and ultimately, which primary airframe it was deployed into.
Critical Issues: Extruded in the absence of a synchronized, digitally role-bound administrative control mechanism, the statistical probability of component mismatching or structural clashes across disparate platforms escalates exponentially. Relying solely on manual worksheets and disconnected ERP peripheral data matrices (often completely deviating from true FIFO constraints) actively liquidates any capability to execute conclusive backward root-cause analyses during critical audits.
|
Problem |
Detail / Impact |
|---|---|
|
Component Mismatching |
The critical operational hazard of erroneously allocating a TB2 structural wing configuration into an AKINCI primary chassis construct. |
|
Authorization Variance |
The unmitigated risk of avionics personnel possessing undocumented authorization to initiate structural mechanics lots within the manufacturing system. |
|
Blind Inventory Status |
Deep informational disconnect spanning the physical state of the shop floor opposed directly against the theoretically available rack hardware. |
|
Audit Unavailability |
The inability to conclusively track a defective component back to its specific production timestamp or designated operator during a revision audit. |
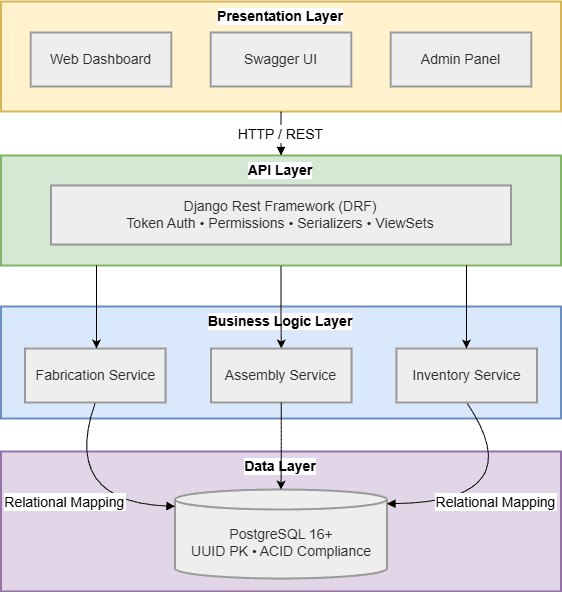
Solution Architecture and Execution
Architectural Approach: A full 3-tier API architecture was mapped out, relying absolutely on role-based security boundaries and deterministic inventory allocations to effectively neutralize asymmetric data management risks.
Applied Methodology
Hardware (UUID) Serialization Process
Every fully manufactured physical component is actively ingested into the database environment formatted exclusively as a UUID. This explicit parameter securely logs production execution times, specific batch typologies, and precise assembly line trajectory assignments ensuring minimal procedural margin of error:
class Part(models.Model):
id = models.UUIDField(primary_key=True, default=uuid.uuid4, editable=False)
part_type = models.ForeignKey(PartType, on_delete=models.PROTECT)
produced_by = models.ForeignKey(Employee, on_delete=models.PROTECT)
production_date = models.DateTimeField(auto_now_add=True)
aircraft = models.ForeignKey(Aircraft, null=True, blank=True, on_delete=models.SET_NULL)
Role-Based Access Control (RBAC) Node
Three heavily separated access roles were actively hardened within the “Production” sector to physically enforce robust duty segregation paradigms:
|
Role |
Permissions |
Constraints |
|---|---|---|
|
Fabricator |
Explicit authority restricted to manufacturing/viewing locally assigned team components. |
Zero operational access bridging into separate team inventory structures. |
|
Assembler |
Secured access explicitly mapped to execution of continuous assembly (platform-level) directories. |
Prevented outright from contributing raw sub-components or hardware elements to the core system. |
|
Admin |
Unrestricted extraction of KPI/P&L status metric reports and dynamic user management control vectors. |
— |
Automated Compatibility Isolation
Configuring a fail-safe framework, the network actively blocks aircraft assembly progressions if human data-input matrices or rogue API requests command conflicting hardware platforms:
def validate_assembly(aircraft_type, part):
"""Halts localized structural crossovers between non-compatible platforms"""
if part.part_type.platform != aircraft_type.platform:
raise ValidationError(
f"{part.part_type.name} part cannot be integrated into {aircraft_type.name} hardware."
)Deterministic FIFO (First-In-First-Out)
Systematically overriding serial production degradation factors, the absolute oldest raw hardware components injected sequentially into the shop floor are prioritized aggressively for assembly querying logic:
def allocate_part(part_type, aircraft):
"""Allocate the oldest historical component directly to open assembly cycles"""
available_part = Part.objects.filter(
part_type=part_type,
aircraft__isnull=True,
is_deleted=False
).order_by('production_date').first()
if available_part:
available_part.aircraft = aircraft
available_part.save()
return available_part
raise StockError("Scheduled integration requirement is functionally out of stock")Soft-Delete Protocols for Audit Logging
Regardless of whether operational components trigger critical revision recalls or are definitively designated as physical scrap assets, items are structurally preserved and exclusively marked (is_deleted) securing uncompromising standard audit compliance logs.
Results and Operational Gains
Quantifiable Output: (Parameters heavily predicated on deterministic simulation readings scaled via PoC testing conditions)
|
Value Focus Area |
Technical Impact |
|---|---|
|
End-to-End Traceability |
Upgraded comprehensive baseline audit qualities by archiving total UUID correlation metrics structurally inside an unyielding digital twin schema. |
|
Hardware Collision Blocked |
Instantly obstructed human-centric data inputs utilizing embedded system verification and rigid backend execution constraints. |
|
Real-Time Inventory Status |
Deployed fractional-second visibility benchmarks via REST API ping interactions, completely bypassing legacy physical stock audits. |
API Integration Architecture (ERP Readiness)
Operating OpenAPI 3.0 frameworks, explicit documentation bridging was formally generated completely optimized for uninterrupted direct socket channels branching outward toward mainstream industrial managerial hubs (e.g., SAP / Oracle grids).
GET /api/parts/ # Index all available active hardware within factory bounds
POST /api/parts/ # Declare standard new ingress component parameters
DELETE /api/parts/{id}/ # Classify component strictly as physical scrap (soft-delete record)
GET /api/aircraft/ # Call active status updates reflecting complete main assembly lines
POST /api/aircraft/ # Initialize new assembly framework matrix directly onto the line
GET /api/inventory/stock-levels # Provide real-time operational hardware stock queries (Live Count)
Related Links
📂 Source Code: Github/aerospace-manufacturing-execution-system
Last Updated: January 2026 | Version 1.0