Technical Knowledge Management and L1/L2 Support Architecture in After-Sales Services

A comprehensive “Technical Competency Program” was strategically designed to completely eliminate the chronic information asymmetry between Customer Services (Tier 1) and the Technical Operations Center (Tier 2/3) within the Turkish operations of a global mobile technology manufacturer. Complex digital security protocols (device locks, bootloader arrays) and intricate fault diagnosis processes were meticulously converted into standardized Standard Operating Procedures (SOPs) explicitly understandable even by non-technical personnel. Through this pipeline, the unnecessary escalation of “User Error” generated problems falsely labeled as hardware faults was permanently prevented at the absolute source.
Project Portfolio
|
Parameter |
Value |
|---|---|
|
Category |
Knowledge Management & Operational Training |
|
Delivery Type |
Technical Training, SOP Development & Process Integration |
|
Role |
Operations Architect |
|
Scale |
~60,000 Mobile Devices, 5 Active Teams (3 Customer Service + 2 Technical Service) |
Current Situation and Challenge
Context: A large-scale mobile device ecosystem currently sporting 60,000+ endpoints in the Turkish consumer market, subjected to an intensive daily customer service demand influx.
Critical Problems:
|
Problem |
Impact |
|---|---|
|
Unnecessary Escalation |
Because customer representatives strictly lacked baseline technical architecture knowledge, they would consistently label even a simple cloud password reset request as a “critical hardware fault” and route it directly to the Operations Center. |
|
Severe Security Risks |
Due to an acute lack of established standard procedures governing device locks and software bypass mechanisms, there existed an extreme high-level risk of unauthorized intervention or dangerous misinformation being relayed. |
|
Operations Team Inefficiency |
The L3 technical repair team was hopelessly wasting vital daily capacity answering rudimentary “How to” password questions instead of focusing on highly complex real hardware repairs. |
|
Inconsistent Communication |
Technical information fed to customers varied hazardously from person to person, deeply fracturing overall brand trustworthiness. |
Solution Architecture and Action Plan
Architectural Approach: Critical technical diagnostic knowledge was forcibly decoupled from individual senior monopoly and permanently structured into robust institutional documentation. A three-layered, end-to-end competency enablement program was meticulously designed.
Technical Documentation (SOP Creation)
Deep technical hardware interventions and software processes were systematically documented step-by-step:
- CMD Terminals: Device cryptographic authentication protocols solely utilizing Fastboot command-line interactions.
- Lock Scenarios: Development of a decisive binary decision tree decisively separating a “Natural User Lockout” from an “Unusual/Malicious Intrusion Lock”.
- IMEI/SN Validation: Firm protocol validating and matching exterior physical box packaging label data against deeply embedded hard-coded device arrays.
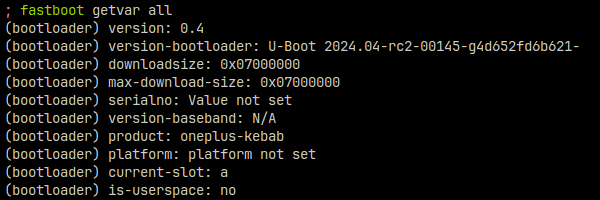
📸 Visual 1: Fastboot command-line diagnostic execution example screenshot (Representative)
Example Terminal Command Output:
(bootloader) product is: A
(bootloader) imei is: 867XXXXXXXXX
(bootloader) sn is: MXXXXXXXX
Training and Competency Enhancement
An exceptionally comprehensive, highly digestible technical awareness training presentation was built from scratch exclusively for the frontline Customer Service (L1) team:
Covered Strategic Topics:
- What exactly is the manufacturer’s isolated cloud account architecture? How is it securely configured? How is a permanent hard reset administered?
- In which precise device lockout escalation scenarios must the ticket be definitively routed to the Technical Operations Center?
- Defining the absolute, unyielding boundaries differentiating supported repair topics from strictly unsupported consumer actions.
📸 Visual 2: Selected slide extracts from the training presentation – “Customer Service Technical Briefing Presentation”
User Issue Classification Processing Matrix:
|
Issue Origin Type |
Resolution Anchor Point |
Case Example |
|---|---|---|
|
Account-Related Flaws |
Customer Service Frontline (L1) |
The master Cloud synchronization password has been forgotten |
|
System Software Flaws |
Remote Operations Support (L1.5) |
The massive OTA Security package update completely failed |
|
Hardware Component Flaws |
Master Operations Center (L2/L3) |
Motherboard micro-short circuits resulting in permanent screen blackout |
Scope Management Boundaries
Baseline support parameters were defined with absolute draconian clarity and immediately transitioned into binding operational directives:
✅ Explicitly Supported Topics:
- Lawful resetting of isolated Cloud account master passwords backed by uncompromised physical proof.
- Identification of structural Push notification communication or localized system refresh logic issues.
- Deep troubleshooting of Global application market (e.g. Play Store) infrastructure crashes.
- Legitimate OEM Lock removal and clearing procedures strictly under validated Invoice and IMEI physical matching.
❌ Excluded Unsupported Topics:
- Flaws arising exclusively from unofficial regional installations (e.g. Chinese market native firmware flashed on global hardware).
- Hardware or software environments structurally manipulated via ROOT access or injection of external Custom ROM packages.
- Demands targeting the unlocking of core Bootloader chains to facilitate custom developer manipulation.
- Code-level crashes emerging strictly from poorly optimized unintegrated third-party applications/gaming engines.
- Intervention requests regarding lost third-party Google Account (FRP) internal recovery workflows.
Results and Operational Gains
Operational Target Gains:
|
Metric |
Measured Impact |
|---|---|
|
Primary Filtering Success |
Basic end-user functional issues fundamentally revolving around passwords, user accounts, and UI settings were successfully absorbed and resolved at a 100% rate during the frontline (Call Center) stage, completely bypassing the hardware center. |
|
Dead Traffic Elimination |
Logistically wasteful NFF (No Fault Found) hardware traffic unnecessarily entering the L2 service layer merely labeled as “Not Defective” was drastically truncated. |
|
Perception Standardization |
Systemic and technical reactionary responses deployed toward the customer base were salvaged from individual personal interpretation and wholly standardized into a rigidly consistent corporate presentation. |
|
L1 FCR Maximization |
Complex “First Contact Resolution” (FCR) SLA measurement metrics were radically elevated, immediately creating a direct positive velocity onto core customer satisfaction scaling. |
Institutional Memory Construction:
- 2 massive cornerstone SOP structural documents (The L1 Fundamental Training Deck + The L2/L3 Advanced Diagnostic Technical Master Guide) engineered throughout the project were permanently archived as foundational operational references.
- This comprehensive documentation core was seamlessly hardcoded into the mandatory formal onboarding pipeline directed at every newly acquired operations personnel.
- Elite, profound technical know-how was successfully extracted and liberated from the isolated experience of veteran seniors, permanently evolving into a 100% scalable corporate asset.
📋 Related Links
🔗 Project Card: VoC Analytics and Critical Quality Crisis Management